
Unfortunately, we can't always trust the messages that arrive in our inbox. A class of criminals called spoofers, or email phishers, make a living by fooling email users into handing over details or downloading malicious attachments. And they only succeed by being as convincing as possible.
According to the cybersecurity and VPN manufacturer Norton, UK consumers lose approximately £4.6 billion to cybercriminals every year, and a big chunk of that comes from spoofing.
However, it's not that hard to protect yourself, and these ten tips should help to learn the skills needed to use email without being ripped off.
1. If it's not from someone you know, it's suspicious
The first rule of detecting email spoofers is to sort out who you can trust from suspicious actors. In general, be very cautious about any emails from organizations or individuals you haven't previously contacted. Unsolicited messages can be the first sign of spoofing activity.
2. Pay close attention to the sender address
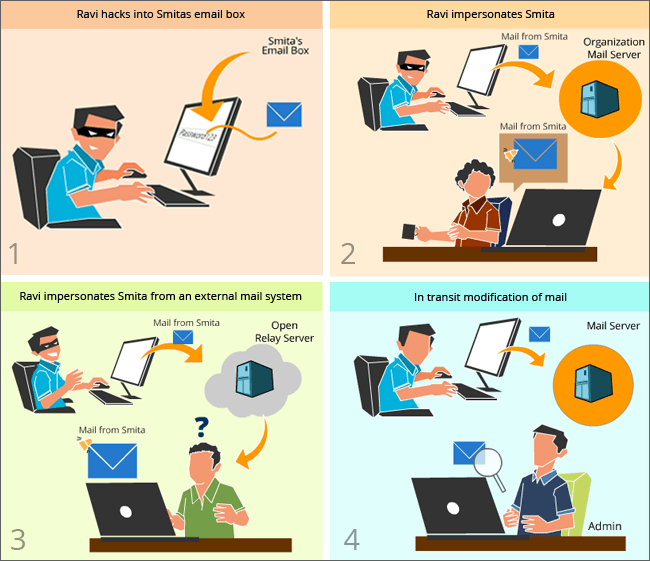
But sometimes, it's easy to be fooled. When people spoof emails, they often use contacts we know but match them up with their email addresses. So while you think you are responding to a friend, you're actually sending information to a spoofer. So check the “sent” line and make sure the address is legitimate. If there are any discrepancies, stay well clear.
3. Be careful when anyone asks for sensitive information
Spoofers want to obtain useful information, such as addresses, social security numbers, or credit card details. That's all they want. But most actual companies won't request this type of information via emails. Instead, they tend to use secure portals. So beware of anyone asking for personal details, and double check their identity before replying.
4. Attachments are bad news
Email spoofers often rely on email attachments. The idea is that recipients click on the attachment, resulting in a malware download which can harvest their information or lock their system. So if you are worried about an unusual attachment, check it out with the sender. Never click blindly hoping for the best.

5. Get used to checking email headers
Every email has a header, containing information about the sender. Email clients have various ways to call up the header, but all should allow you to do so. The information it holds will show the source of any email, unmasking most spoofers in the process.
6. Learn how to read emails slowly
One of the biggest mistakes people make when falling for spoofers is clicking on emails too quickly. Most of the time, we can learn a lot by merely hovering our cursor above certain parts of the text – instead of clicking through. When one click can lead to a ransomware attack, it pays to be cautious.
7. Be a spelling hawk
Bad grammar and poor spelling is sometimes the only way to tell whether you're being spoofed. Reputable companies tend to be pretty sharp where language is concerned, but phishers aren't always so meticulous (and may well not speak English as a first language). So take a note of errors. They could well be telling you something vital about the source of the email.
8. Consistency matters
Skilled spoofers can get past many of the filters we've noted already, but they struggle to imitate the way we communicate. For instance, each company will have its own corporate tone and approach of greeting customers. And they tend not to divert from that style too much. But phishers sometimes forget to research this. So if their tone isn't right, stay clear.
9. Are contact details lacking?
Most of the time, legitimate emails from companies or friends will include ways to respond to the sender – often multiple ways such as email, phone, websites, or social media. If there is one single email to reply to, that's a major red flag.
10. If it's too good to be true, it usually is
Some of the most profitable email spoofs try to trick customers into thinking they have been offered amazing deals. This works well because reputable companies rely on email marketing. So it can be tough to separate genuine from criminal emails.
As a rule, be cautious. If the deals promised are ridiculously generous – they are likely to be fraudulent. And if you think they are fine – get in touch. Genuine companies will be happy to explain why their prices are so low. Phishers will probably ignore you.
After mastering how to spot phishing, don't stop there!
By now you should have a fairly good idea of how to spot rogue emails and defeat the aims of phishers. But the answer to the question of what is cyber security goes well beyond phishing. From keeping your systems clean of malware to learning how to use VPN tools, there's a whole range of things that users need to be aware of.
So when you're confident that you're an ace phishing detector, go a little further. You'll soon master the whole range of cybersecurity practices required to enjoy the internet as safely as possible.

